Cyber Heads Up: “BadSuccessor”—A Critical Active Directory Privilege Escalation Vulnerability in Windows Server 2025
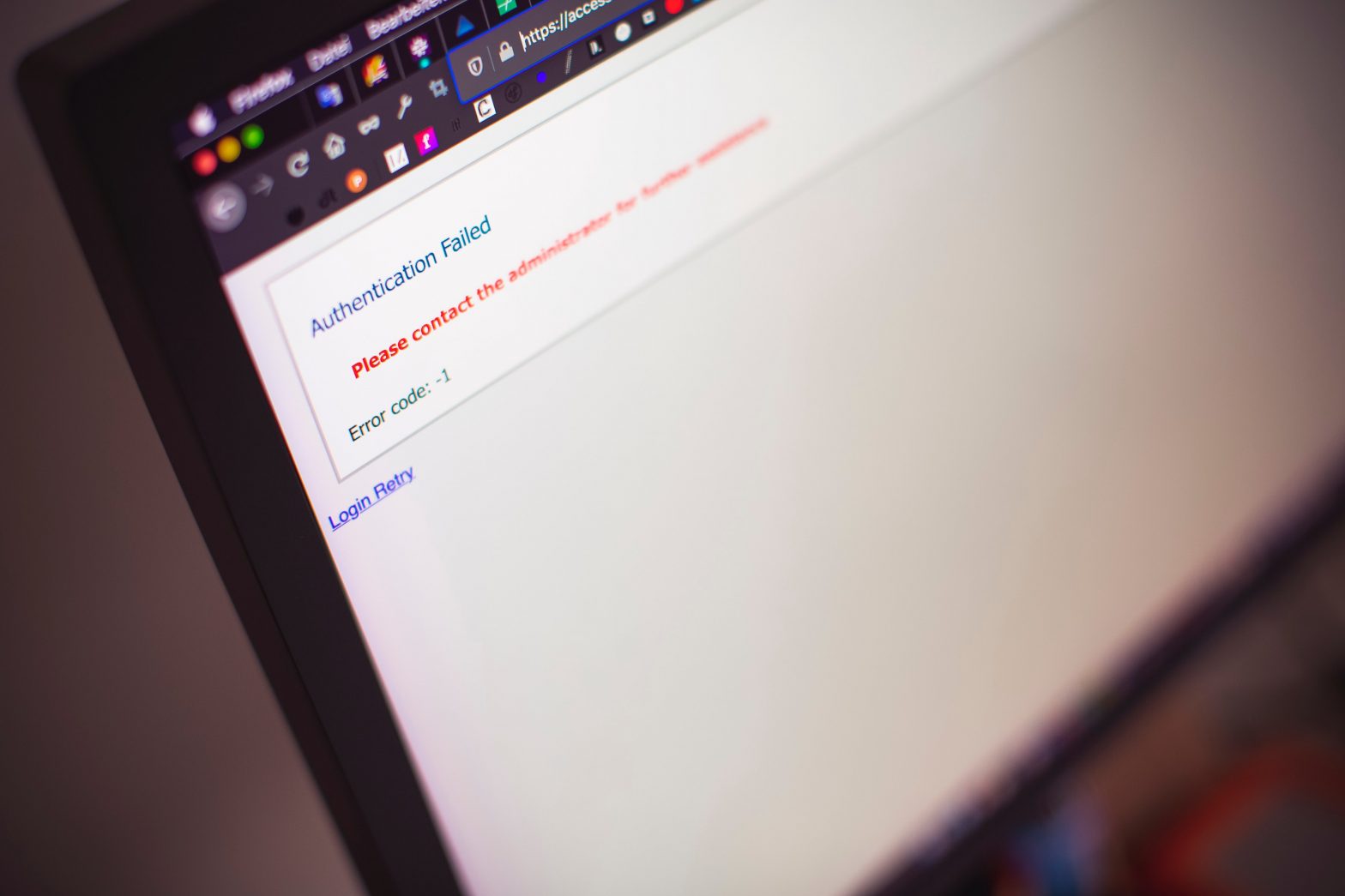
Overview: Akamai researchers have identified a significant privilege escalation vulnerability in Windows Server 2025, termed “BadSuccessor.” This flaw exploits the newly introduced delegated Managed Service Accounts (dMSAs) feature, allowing attackers to impersonate any Active Directory (AD) user, including domain administrators, without altering existing accounts or group memberships. Key Details: Impact: Exploitation of BadSuccessor can lead… Continue reading Cyber Heads Up: “BadSuccessor”—A Critical Active Directory Privilege Escalation Vulnerability in Windows Server 2025