Overview
If you haven’t already heard about these in the press, we’re here to tell you about them. On Tuesday of this week (14 January 2020), the U.S. Department of Homeland Security’s Cybersecurity and Infrastructure Security Agency (CISA) released advisory number AA20-014A: Critical Vulnerabilities in Microsoft Windows Operating Systems.
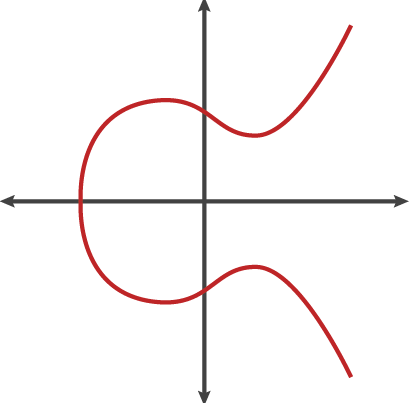
- CryptoAPI spoofing vulnerability – CVE-2020-0601: This vulnerability affects all machines running 32- or 64-bit Windows 10 operating systems, including Windows Server versions 2016 and 2019. This vulnerability allows Elliptic Curve Cryptography (ECC) certificate validation to bypass the trust store, enabling unwanted or malicious software to masquerade as authentically signed by a trusted or trustworthy organization. This could deceive users into installing software that looks like it oroginated from a trusted source or thwart malware detection methods such as antivirus. Additionally, a maliciously crafted certificate could be issued for a hostname that did not authorize it, and a browser that relies on Windows CryptoAPI would not issue a warning, allowing an attacker to decrypt, modify, or inject data on user connections without detection.
In a rare move by the U.S. National Security Agency, the vulnerability, dubbed “Curveball”, was disclosed to Microsoft rather than the the agency weaponizing it for use in its cyber espionage mission.
- Multiple Windows RDP vulnerabilities – CVE-2020-0609, CVE-2020-0610, and CVE-2020-0611: These vulnerabilities affect Windows Server 2012 and newer. In addition, CVE-2020-0611 affects Windows 7 and newer. These vulnerabilities—in the Windows Remote Desktop client and RDP Gateway Server—allow for remote code execution, where arbitrary code could be run freely. The server vulnerabilities do not require authentication or user interaction and can be exploited by a specially crafted request. The client vulnerability can be exploited by convincing a user to connect to a malicious server.
These vulnerabilities are so severe that CISA used its statutory authority to publish an emergency directive ordering all U.S. Federal agencies to patch their systems by 5:00 PM EST on 29 January 2020. By today (17 January 2020 at 5:00 PM EST), all Federal agencies were required to submit an initial status report to CISA documenting their progress.
AA20-014A can be found here: https://www.us-cert.gov/ncas/alerts/aa20-014a
CISA’s Emergency Directive can be found here: https://cyber.dhs.gov/ed/20-02/
NSA’s Cybersecurity Advisory can be found here: https://media.defense.gov/2020/Jan/14/2002234275/-1/-1/0/CSA-WINDOWS-10-CRYPT-LIB-20190114.PDF
A detailed analysis of the vulnerability for crypto/math geeks can be found here: https://medium.com/zengo/win10-crypto-vulnerability-cheating-in-elliptic-curve-billiards-2-69b45f2dcab6
Assura’s Take
It’s common that severe vulnerabilities are disclosed by software publishers, but this one is particularly noteworthy because of the seriousness with which the NSA(!) and CISA takes them. NSA is not in the business of disclosing vulnerabilities — it’s in the business of finding and using vulnerabilities to project power in cyberspeace to support US policy and military goals and objectives. So it’s telling about the level of severity of this flaw that they would override that aspect of their mission in the case of CVE-2020-0601.
The bottom line is that Assura strongly recommends installing the necessary patches as soon as possible to avoid any active exploitation. Consider these emergency patches and get them in. They have had several days to “burn in” in the wild without reports of widespread issues. Currently, there are no known exploits occurring in the wild, but proofs-of-concept have been developed, which means it is only a matter of time before the real bad guys weaponize them.
If you’re an Assura Virtual ISO client and have any questions about this, please contact your Virtual ISO. If you’re an Assura Managed SIEM client, our SOC continues to remain vigilant and on heightened alert for suspicious behavior. If you have any questions about mitigating these risks, please feel free to reach out to your Assura point-of-contact or via the web form on our site.