Higher education institutions store vast amounts of sensitive information, including student and personnel records, financial details, and proprietary faculty research. This accumulated data makes schools an ideal target for bad actors in the modern cyberscape, yet such dangers are further heightened by colleges’ and universities’ unique technology requirements. Therefore, implementing reliable security compliance solutions is… Continue reading Safeguarding Student and Faculty Data: Cybersecurity in Higher Education
Category: Blog
SLED Cybersecurity Threats in 2025: What You Need to Know to Stay Ahead
While digital transformations have given state, local, and education (SLED) organizations unprecedented operational flexibility, threat actors are looking to exploit their new vulnerabilities. A virtual frontline has formed, and cybersecurity measures must defend against a rising tide of cyber threats. Ransomware attacks, phishing schemes, IoT vulnerabilities, and more make it imperative that SLED organizations’ leadership… Continue reading SLED Cybersecurity Threats in 2025: What You Need to Know to Stay Ahead
Top Cybersecurity Compliance Issues Businesses Face Today
As organizations increasingly rely on digital infrastructure, the stakes have never been higher. Cybersecurity compliance is necessary to safeguard sensitive data, maintain customer trust, and avoid costly fines. With a constantly shifting threat landscape, evolving regulations, and the rise of new technologies, businesses must prioritize cybersecurity posture improvement to stay ahead of the curve. Assura… Continue reading Top Cybersecurity Compliance Issues Businesses Face Today
How SLED Organizations Can Enhance Cybersecurity Compliance Before Year-End
As the year comes to a close, State, Local, and Education (SLED) organizations must resharpen their focus on strengthening their cybersecurity defenses. With the growing complexity of cyber threats and the need to safeguard valuable data, it’s vital for SLED organizations to stay ahead of risks. Cybersecurity compliance consulting services offer guidance in navigating state… Continue reading How SLED Organizations Can Enhance Cybersecurity Compliance Before Year-End
Unify & Conquer: How Open XDR Streamlines Your Security Operations
In today’s rapidly evolving cybersecurity landscape, staying ahead of threats requires innovation, agility, and robust partnerships. At Assura, we’re dedicated to providing our clients with the most advanced and effective cybersecurity solutions. That’s why we are thrilled to announce our latest collaboration with Stellar Cyber, leveraging their cutting-edge Open XDR platform to enhance our security… Continue reading Unify & Conquer: How Open XDR Streamlines Your Security Operations
Cybersecurity Tips from Assura’s VISO Bunch
Assura’s Virtual Information Security Officers (VISO) deliver a complete solution for both cybersecurity and compliance. Also referred to in the industry as Fractional Chief Information Security Officers (CISO), their expertise is an invaluable asset to our clients. Watch the video below to meet some of the VISO team as they give cybersecurity tips on topics… Continue reading Cybersecurity Tips from Assura’s VISO Bunch
Cybercrime Victim Resources for Individuals
At Assura, we protect businesses and government organizations but know that anyone can be a cyberattack victim. Below are resources that we recommend in the unfortunate situation of a personal cyberattack (links known to work as of the date of publication): Federal Trade Commission ReportFraud Federal Trade Commission Identity Theft and Online Security Federal Trade… Continue reading Cybercrime Victim Resources for Individuals
Assura’s Top 5 Misconceptions about Penetration Testing
With the increasing number of organizations now seeking penetration testing due to regulatory requirements, more and more companies are claiming to offer a service that checks this box. Assura wanted to help clarify some of the top misconceptions you may encounter when searching for a penetration test. We hope this demystifies the process and helps… Continue reading Assura’s Top 5 Misconceptions about Penetration Testing
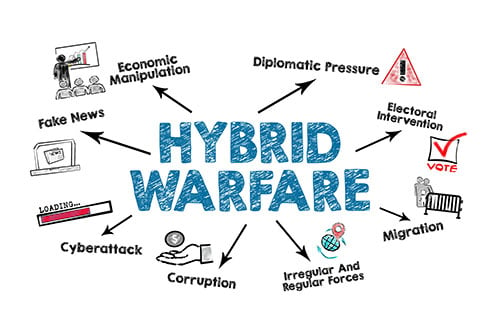
Thoughts on the Cyberwar Between Russia and Ukraine (and the Rest of the World)
In the early 2000s, I began to hear colleagues talk about cyber warfare and declare that the next battlefront wasn’t going to be fought with “boots on the ground” but in cyberspace. These statements had credibility because those saying this were retired high-level officers from the US armed forces. If anyone knew about the future… Continue reading Thoughts on the Cyberwar Between Russia and Ukraine (and the Rest of the World)
Fractional Information Security Officer: 3 Questions to Ask When Determining if Your Business Needs One.
Every week – if not every day, seemingly – an organization makes headlines for experiencing a cyber-attack. Sadly, for every Microsoft Exchange crisis, there are scores of small and medium-sized businesses (SMBs) wrestling with a data breach. While SMBs have been known to leverage fractional C-suite consultants for needs like accounting and HR, in the current… Continue reading Fractional Information Security Officer: 3 Questions to Ask When Determining if Your Business Needs One.